According to a payment facilitator, CCV, mobile commerce represented 48 percent of digital sales by 2017, and the numbers are increasing across the board. Because smartphones are becoming a huge part of everyone's lives, more and more people are adopting mobile payment services such as Mobiamo. But is Mobiamo safe?
It doesn't collect too much information from you, as all it needs is your mobile number. Secondly, it verifies transactions, much like how two- or multi-factor authentication works. Both of these mechanisms help make Mobiamo inherently safer than other forms of payments.

How does Mobiamo help to keep your money safe even as you start out using mobile payments? Are there things that you should know?
Mobiamo Only Collects Your Mobile Numbers
Not so fun fact: hackers were able to obtain more than 446.5 million personal financial records in 2018. Usually, they stole your financial details from businesses you patronize and even healthcare companies.
The cost of credit card fraud can reach $20 billion this year, and more than one out of three people will fall victim to identity theft or credit card fraud at least once in their lifetime.
The thing is once you give your credit card information to a retailer or a service provider online, you pretty much made yourself a target for identity thieves and hackers. You will have no control over how these establishments store and secure your details.
Their systems can get hacked or infected by malware, their employees can get duped by a phishing e-mail, or they can even sell it. There is no guarantee. For instance, the Equifax hack in 2017 showed that even such a big company could be breached, resulting in 147 million having their personal information compromised.
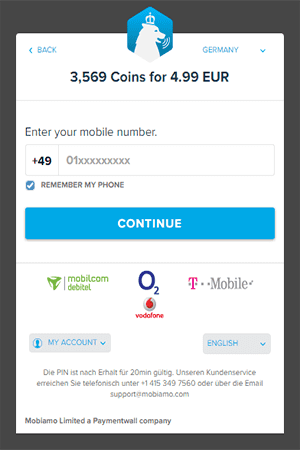
Now, what if you can send or receive payments without having to send over your credit card details? Mobiamo only needs you to have a mobile phone that allows direct carrier billing, premium SMS, or value-added services.
You are not required to have a credit card or bank account to use the service. And if you do have one, you're not required to link it to your Mobiamo account.
No Tokens Needed
Unlike other mobile payment systems such as Apple Pay, you don't even have to deal with tokenization. Tokenization converts your credit card details and other pieces of information into a random string of numbers.
When you pay with these systems, the token gets sent, not your personal details. But while tokens are useless even when a hacker gains access to them, your credit card details are still stored somewhere for authentication purposes and it can still be hacked.
With Mobiamo, you don't have to provide your credit card details or bank account numbers to anyone. All you need is a working cell phone number. If you're using a prepaid number, you will also need to make sure that you have enough balance to cover the payment.
Authentication Works Like 2FA
But how does Mobiamo authenticate your payments? Once you have input the payment details into the Mobiamo widget, you will get an SMS message with the PIN code. You will need to enter this PIN code into the widget to authorize your payment.
If you are using your mobile phone to make a payment, the system will verify the number you inputted with the number you're using. If it matches, you no longer have to input any PIN, and the payment goes through.
If that whole process sounds familiar, it's because it's the same two-factor authentication that you might be using with your e-mail and other accounts.
What Is Two-Factor Authentication?
Two-factor authentication is when you have an additional layer of security. This way, even if a hacker does get hold of your user name and password, they will still need to provide another type of information before they can gain access.
Some things that can be used for two-factor authentication can be:
- Something that you know: a PIN, secret questions, or a keystroke pattern
- Something that you have: a smartphone or hardware token
- something unique to you: Fingerprint, iris, or voice scans
The most common form of two-factor authentication that is widely used today is when you sign on to your account, and the system sends you a code or PIN that you will need to enter before you can access the account.
Mobiamo's system sends you an SMS message to verify if you have possession of the mobile phone number that you entered into the widget. The SMS message will contain an alphanumeric code that you will need to enter into the widget before your payment is processed.
Two-Factor Authentication Is Effective
Various statistics point to how effective two-factor authentication is. Did you know that while 91 percent of users know how dangerous it is to reuse passwords for two or more sites, 61 percent still reuse their passwords?
And the effects are obvious: 81 percent of data breaches are due to weak, stolen, or reused passwords.
Two-factor authentication can stop several types of attacks that are related to compromised user credentials. According to the Information Technology Services of the University of California at Santa Cruz, using two-factor authentication can stop phishing, keyloggers, credential stuffing, man-in-the-middle attacks, and brute force attacks.
Google also reports that two-factor authentication can stop all automated bot attacks.
Other Considerations
Apart from not requiring you to give out your credit card details and other personal information except for your mobile number, and using a proven authentication technology, some things can help you gauge just how safe Mobiamo is.
Carrier Billing
At its heart, Mobiamo is a carrier billing payment system. If you're using a prepaid number, you must have enough balance for the payment to push through. If you have a postpaid line, the payments will be reflected on your next bill.
One of the biggest advantages of carrier billing is that you don't have to worry about fraud unless you lose your phone, which is the only way that your payments can be authorized.
The good news is that carriers usually impose a limit on how much you can bill to your account. For instance, T-Mobile allows you to bill up to $80 to your account per month. Compare that to the $450 that the average identity theft victim paid in 2016.
So even if you do lose your phone and the thief was able to figure out your PIN and lock patterns, the damage you incur will be very limited.
Your Smartphone: The Weakest Link
With no information to steal and no servers to hack into, Mobiamo reduces the number of attacks that can be carried out for hackers to steal your identity or your financial details. Carrier billing also brings some degree of protection when it comes to keeping your identity private, as even merchants may not even know who you are, even if you buy from them.
However, you can still fall victim to fraud if you don't protect your smartphone. Around 70 million smartphones are lost every year, and making things worse is that most people don't even care to secure these devices. According to this Pew Research Center study, 28 percent of smartphone users do not use any kind of lock screen on their phones.
If you want to have a safer experience with mobile payment systems such as Mobiamo, make sure that you use your phone's security systems to make it more difficult for thieves to use it to steal from you.
Mobiamo Is Safe
Mobiamo allows you to avoid the security pitfalls that you have when using credit cards as a way to pay. They also do not require your data aside from your phone number to approve and facilitate your payments.
Mobiamo also relies on carrier billing and value-added services to process your payments. If you don't lose your phone, and if you have enabled its security options such as PIN codes, lock patterns, or fingerprint scanning, you don't even have to worry about other people being able to approve payments via Mobiamo without you knowing.
Share this with your friends
Related Articles
Here are some articles you might be interested in:
What questions do you have?
I make sure to answer them as soon as possible!
- Copyright © 2020 YOU are safe online.
- All Rights Reserved.