25 Tips to Stay Safe on Public WiFi (+ BONUS recommendations)
19 min read by Bogdi
published 2 ani în urmă, updated un an în urmă
Have you been wondering how to stay safe on public WiFi? If you’re in a public place and you need to connect to the internet, you check your laptop or tablet for available connections and, chances are, you’ll find a list of open networks. Which one should you choose? Is it safe to connect to any open network?
Public WiFi networks are rarely as secure as private networks. While it is possible to use these unsecured networks safely, it’s important to have your security software up to date and understand how to avoid becoming the next victim of identity theft. Read on to learn more about public WiFi networks and how to use them safely.
Is it Safe to Use Public WiFi?
Public WiFi networks are open, meaning that anyone can connect to them with a click of a button. Whereas private networks often have various levels of security in place, open networks do not. Most open networks don’t even require a password to connect to them.
When you use public WiFi, everything you do online over unsecure connections could be intercepted. Most people, of course, don’t know how to access it and don’t care. But hackers and identity thieves often lurk around public WiFi, attempting to spying on people browsing the internet.
So no, using public WiFi isn’t as safe as using a private network.
That said, there are steps you can take to increase your security even when using public WiFi. Not all public networks are created equal. Some are more secure than others, and some even have security measures of their own in place. If you know which networks to use, take security precautions beforehand, and understand what not to do online while using public WiFi, you can greatly increase your chances of avoiding security breaches.
25 Public WiFi Safety Tips
Let’s take a look at some of the things you can do to use public WiFi safely.
Security Measures
1. Understand Potential Security Threats
One of the best ways to avoid security threats is to know what you’re up against. There are several different ways identity thieves and hackers use open networks to prey on the unsuspecting. Some of their methods include:
- Offering a hotspot they own as an open network. It may look like any other open network, but in reality, it allows the hacker to access every site you visit and, potentially, all the information you enter.
- Spying through an open network. When you use an open network, anyone else using that network can see what you’re doing online. Of course, most people won’t go looking, but hackers may use open networks to spy on unsuspecting users.
- File sharing. Sharing files over an open network is one way hackers use to infect your computer with viruses.
- Fake system updates. Hackers can create fake system alerts and make them pop up on your computer. If you click on the alert message, it will give your computer a virus.
Be aware of these potential threats even if a network looks dependable. No open network is entirely risk-free.
2. Keep Security Up to Date
While you should never perform any system updates while using an open network, make sure you have some form of antivirus software installed and keep it updated regularly. Life Hacker recommends using both an antivirus utility, such as Avira or Sophos, and an antimalware utility, such as Malwarebytes.
Regardless of the security system you use, the important thing is to keep it running. If you allow it to expire or don’t run the latest updates, your computer could be left open to security breaches. This is especially true when using an open network.
3. Use a VPN
VPNs, or “virtual private networks,” are a popular type of software that route your connection through encrypted servers even when you’re using an open network. This means that your browsing history and any information you enter is blocked from anyone who might try to access it, keeping your internet activity completely private.
You can also use VPNs to access banned or restricted websites without being detected, which is great if you’re traveling in a country with a lot of internet restrictions.
Later in this article, we’ll take a look at the following best VPN services on the market:
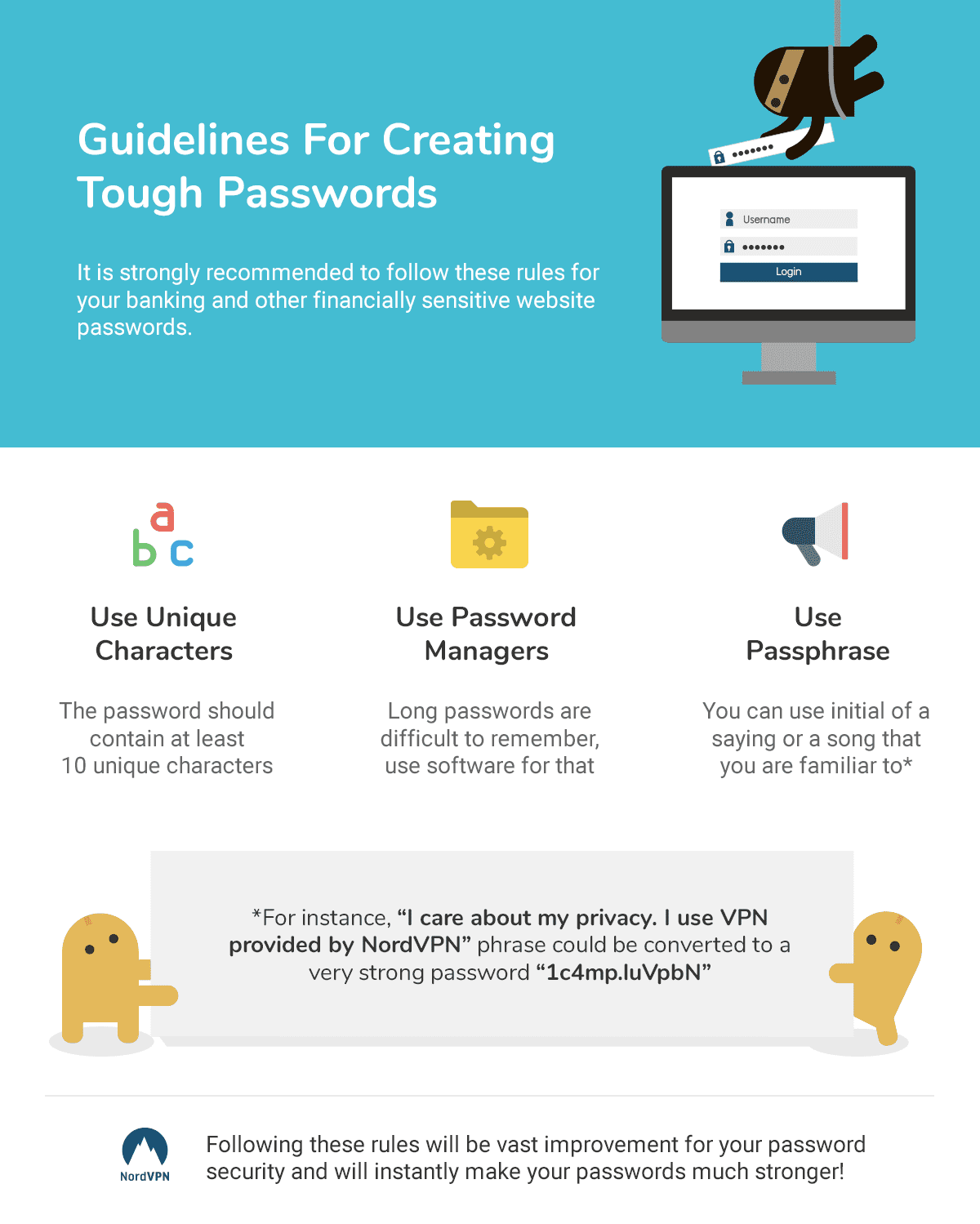
4. Use a Password Manager
Creating a separate, strong password for each site you use is essential for reducing your chances of getting hacked, whether using an open network or not. But with so many sites asking you to create a username and password, how are you going to remember which password goes with which site? For that matter, how are you ever going to come up with that many unique passwords?
That’s where a password manager comes in.
Password managers are essentially little secretaries--they’re software that store and manage all your passwords. They can even help you create new passwords.
While password managers are a great way to create and secure your passwords, they are not all created equal. Later in this article, we’ll look at the following dependable password managers:
5. Use HTTPS as Much as Possible
Whenever using an open network, try and stick to the sites that have “HTTPS” in their web address rather than just “HTTP”. The “S” stands for “secure”, and these types of websites come with a little padlock symbol on the left side of the address bar. HTTPS sites are encrypted so that any information shared is kept private.
Though HTTPS can’t prevent a hacker from seeing the sites you visit on an open network, the HTTPS encryption will at least block them from gaining access to passwords or any personal information shared through the site.
6. Encrypt your Device
You can use encryption to secure your device as well. Though it isn’t completely failproof, it comes pretty close.
Encryption is a process of scrambling your data so it’s harder to read and, thus, more difficult to hack. By encrypting your laptop, you can add an extra layer of security to keep hackers from accessing important files or documents stored on the disk.
Mac laptops are generally the easiest to encrypt, but most PCs allow pretty hassle-free encryption as well. The methods for encrypting will depend on your type of computer and operating system, but you can generally set up encryption within a few minutes through your laptop’s settings.
Network do’s and don’ts
7. Use Semi-Open Networks if Possible
Some open networks, especially those offered by businesses and restaurants, require a network key to access. These networks are generally more secure than regular open networks because it takes one or two extra steps to connect to them. These types of networks are referred to as “semi-open” networks.
If you have a choice between choosing an open and a semi-open network, always go with the semi-open network. You may have to ask an employee for the network key and some businesses may require you to make a purchase before allowing you to connect. But the few extra minutes or dollars of hassle will pay off in the form of a more secure network.
8. Use Only Reliable Open Networks
If you’re in a public place such as an airport or sports venue, there may be several open networks available. Learn to recognize the difference between the “good” open networks and the “bad” ones.
As an example, certain merchants within a large venue may offer an open network for their patrons. They will likely include their company name in the name of the network.
It’s more secure to connect to one of these merchant-based networks than some overarching network covering the whole venue. For one thing, smaller, company-based open networks will likely have fewer users; for another, they are less likely to be run by hackers.
9. Read the Terms and Conditions
Or at least scan them, looking for anything that sounds suspicious or questionable. You don’t have to understand all the technical language, but you should be able to spot anything that doesn’t seem quite right.
If a network doesn’t have any terms and conditions, better to search for a new network.
10. Never Give Out Personal Info
This goes without saying. If any open network asks for your full name, email address, phone number, or any other personal information, do not enter it. Choose a different network. A reliable network will not require you to provide any personal information in order to connect. If you are asked for your personal information, or any sensitive details, the network is likely being run by a hacker.
When Using an Open Network
11. Disable All File Sharing
Since file sharing is one way hackers can infect your computer, it’s important to make sure all file sharing and access options are turned off before connecting to an open network.
You’ll find file sharing options in your laptop’s settings. On a PC, they’re usually under “sharing settings,” “file access,” or something similar. On a Mac, you’ll find them under “system preferences” and “sharing.”
Speaking of Macs, you’ll also want to change your AirDrop settings to contacts-only, or disable it completely.
12. Only Use Open Networks for Certain Things
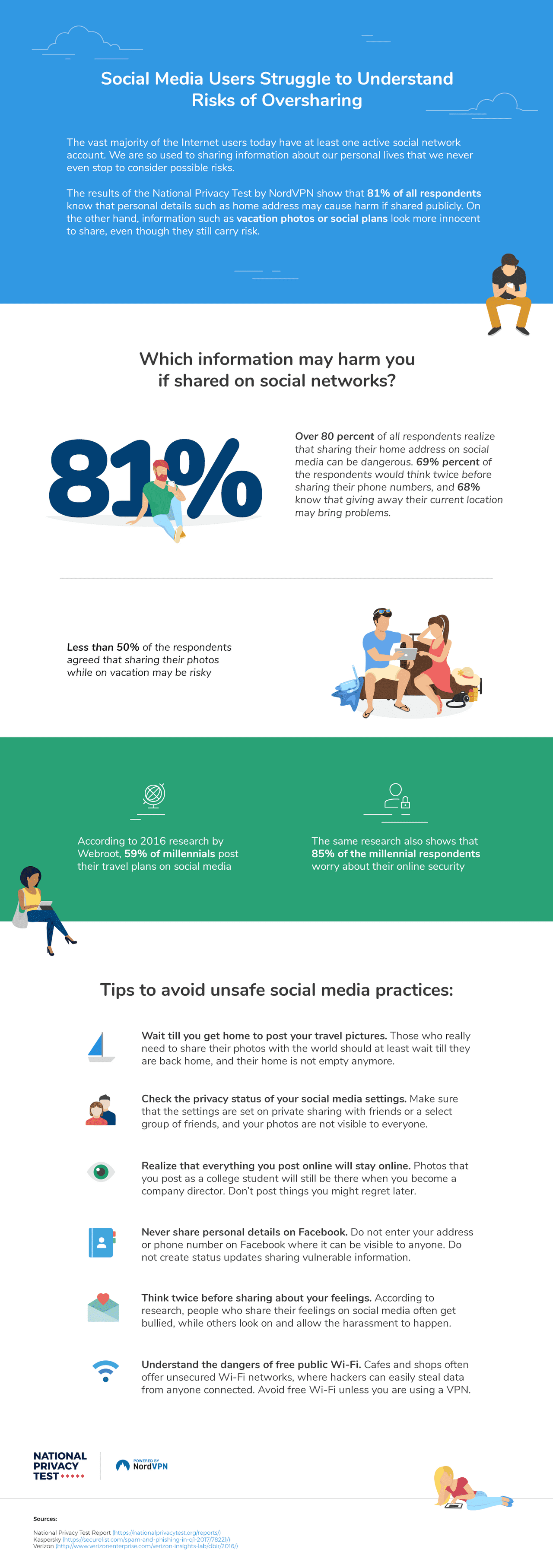
Think about the sites you’re visiting and the types of information you’re providing. Using social media will require you to enter a password, whereas when you check your bank account, you may have to enter an account number and PIN, and you’ll be exposing your finances to whoever may be watching.
Remember, hackers can see everything you do on an open network that is not encrypted.
Some things you can do fairly safely on an open network include:
- Checking Facebook
- Playing music on YouTube or Spotify,
- Scrolling the web
Things you shouldn’t do on an open network include:
- Checking your bank account
- Buy something off Amazon
- Submitting a job application
13. Never Download or Install Anything Through an Open Network
Avoid doing any type of system upgrade while using open WiFi. Don’t click on any pop-ups, and don’t install or download anything. This includes browser updates, email attachments, and any other file, whether you know where it’s coming from or not.
No matter how real it looks, clicking on anything to install or download may allow hackers to access your information via viruses and malware.
14. Keep Browsers and Software Up to Date
Always allow your laptop to update on a secured network, and make sure it updates on a regular basis. An updated operating system, browser, and other software are less likely to become infected with viruses.
15. Use Secure Browser Extensions
Browser extensions such as uBlock Origin and Disconnect provide another type of security. Whereas antimalware and antivirus software protects your computer against things you may download, browser extensions offer protection as you search the web.
Browser extensions can not only prevent ad pop-ups, but can be customized so you choose which types of ads are blocked and which ones aren’t. They can also protect you from network hijackings, which can present a threat even if you’re using a secured network.
16. Use Apps with Caution
If you’re using a phone or tablet on an open network, or if you use apps on your laptop, be aware that any apps you use may put you at risk. Not all apps are secure, and while some may use HTTPS, this isn’t true across the board. It’s better to assume your apps are insecure and use your browser to check them for security features before using them on an open network.
17. Use Strong Passwords
We all know passwords are one of the first lines of defense against hackers and identity thieves. When creating a new password, be sure to mix things up a bit -- use both upper and lower case letters, numbers, and symbols.
It’s also okay to get creative. You can spell words backwards, alternate lower and upper case for every letter, use multiple short words separated by numbers or symbols, and even add in spaces if you want. The possibilities are endless.
The more unique your passwords, the less likely a hacker is to figure them out.
18. Enable Two-Step Verification
Some sites may give you the option of a two-step login process. Two-step verification usually involves entering your password, then entering a code that is sent to you via email or text message. This extra step gives you a second layer of protection even if your password is compromised.
Some sites that allow two-step verification include:
- Gmail
19. Use Social Media with Caution
Always be careful about posting your personal details, location, contact information, etc. on social media. Remember that when you’re on social media while using public WiFi, a hacker can see everything you’ve posted and can use your personal details to figure out your passwords.
20. Always Log Off When You’re Done
Anytime you log into a website or app while on an open network, be sure and log off when you’re finished using that site. This goes for social media sites, emails, Amazon, school or library accounts, and any other site that requires you to log in.
Logging out when you’re done is a good general practice for shared devices such as public computers, and the same holds true for public networks.
21. Turn Off WiFi when Not Using
Once you’re done using an open network, turn off the WiFi. For most computers and tablets, this is a simple matter of clicking a button. Turning off the WiFi is the best way to ensure hackers can’t find their way into your device when you’re not using it. Even if you’re no longer online, your device may still be visible to hackers if you are still connected to the network. Play it safe and get off the public network as soon as possible.
22. Disable Automatic Connection
Your device may be set up to remember the networks you connect to. If this is the case, it may automatically connect to an open network the next time that network is available.
To prevent unwanted connections, look for the following buttons or checkboxes in your network and internet settings:
- “Connect automatically” (Uncheck this box before connecting to the network)
- “Forget the network” (Check this box)
- “Remember networks this computer has joined.” (Uncheck this box)
23. Beware of Anything that Looks Suspicious
There are endless ways hackers may try and get at your personal information, and it’s impossible to think of every scenario beforehand. When using an open network, stay alert for anything that seems strange or not quite right. If you feel that your privacy is threatened in any way, don’t ignore that feeling.
Using public WiFi is a bit like defensive driving -- if you view every vehicle on the road as a potential threat, you’re more likely to drive with caution and react to impending accidents before they happen.
24. Keep Important Documents Saved Elsewhere
If you use open networks on a regular basis, you may want to consider moving important documents to a desktop computer on a secured network. Even if you avoid public networks for the most part, consider what important documents you have saved on your laptop before allowing a new connection.
Some documents you may want to keep somewhere other than your laptop include:
- Tax form
- House closing documents
- Financial spreadsheets
25. Use Your Own Hotspot Whenever Possible
A lot of phone and internet plans include a free hotspot. If you have a hotspot on your phone that you can connect your laptop to, that will be a much more secure option than using an open network. Or if you have your own personal hotspot on your laptop, that’s even better.
Best Password Managers
Using a password manager is a great way to increase your security when using public WiFi. Password managers keep track of all your different passwords and to generate new passwords if you run out of ideas. Some password managers are free, while others charge a monthly or yearly usage fee. Let’s talk about some of the best password managers on the market.
Keeper Password Manager
Keeper Password Manager offers both free and paid subscriptions. The free service is compatible with a single device, while the paid service can be used across unlimited devices.
Keeper offers unlimited password storage for each device that uses it. It offers three subscription plans, from the free subscription up to the Family plan, which costs $74.99. All plans include autofill password capabilities, payment card storage, and two-factor authentication.
Depending on the specific plan, you may also have access to special features such as dark web protection, secure file storage, and encrypted messaging.
Pros:
- Unlimited password storage
- Various plans
- Payment card storage
Cons:
- Free plan limited to one device
NordPass
NordPass is a password manager created by the company that produces NordVPN, being their newest product.
NordPass has some of the best features available in the password manager program market. Apart from being free with unlimited password storage, NordPass is simple and easy to use for any customer. In short, NordPass’s features set it apart from other password management applications.
Pros:
- Biometric identification system
- Unparalleled support
- Easy to share with family or coworkers
Cons:
- Lacks automatic password changer
The password manager I use and recommend
From the people that made NordVPN, a truly secure password manger.
Check out NordPass* By using the above links, you help make the internet a better place. If you decide to buy, this web page will be credited with a small commission, at NO EXTRA COST to you. Let's make the internet a better place, together!
* By using the above links, you help make the internet a better place. If you decide to buy, this web page will be credited with a small commission, at NO EXTRA COST to you. Let's make the internet a better place, together!
LastPass
LastPass offers one of the best free plans. It also offers two paid subscriptions, but many users consider the free subscription to be every bit as good as most paid password managers on the market. Its paid subscriptions, especially the Premium option, can get pretty pricey.
LastPass can be used across all your devices and allows unlimited password creation. It is compatible with all types of devices. Some of its features include storing digital records, secure shopping and sharing, built-in password generator, and dark web monitoring.
Pros:
- Unlimited passwords and devices
- Best free plan
- Great features
Cons:
- Pricey paid plans
Bitwarden
Like LastPass, Bitwarden's free plan allows an unlimited number of passwords on an unlimited number of devices. It’s an open-source password manager, meaning there are a large number of software developers constantly working on it and improving the security features.
Bitwarden’s paid subscriptions are less expensive than a lot of password managers, costing just $10 a year for premium and $40 a year for family plans. It also has business plans available. Bitwarden encrypts all the information on your device, making it harder to hack. It offers all the usual features and is highly customizable. This makes it an ideal choice for more tech-savvy people.
Pros:
- Unlimited devices and passwords
- Open-source
- Inexpensive paid plans
Cons:
- Difficult to use
Sticky Password
Sticky Password's free plan can’t sync between devices, but it does allow unlimited passwords across unlimited devices. It comes with some unique features including biometric login, compatibility with eleven different browsers, and the ability to download onto a USB and use it with any device.
Sticky Password also offers a premium subscription for $29.99 a year which includes syncing devices, secure password sharing, and cloud backup.
Pros:
- Unlimited devices and passwords
- Biometric login
- USB compatibility
Cons:
- Free plan can’t sync devices
Dashlane
Dashlane is one of the best overall password managers you can find. It offers great features including a one-click password changer and security breach notifications. The free plan will only store 50 passwords on one device, but the premium plan allows unlimited passwords across unlimited plans. The premium plan also includes a VPN and you can sign up for a 30-day free trial so you can try it risk-free.
Pros:
- User-friendly
- 30-day free trial of premium plan
- Great features
Cons:
- Free plan limitations
Best VPN Providers
Because VPNs essentially create your own private, secured network, they are a must-have if you have to use public WiFi. Let’s take a look at some of the best VPN providers.
ExpressVPN
ExpressVPN is frequently considered the best overall VPN on the market. ExpressVPN boasts over 3,000 servers across 94 countries, making it fast, secure, and reliable wherever you go. It is easy to install and easily unblocks streaming services that are often blocked when you’re out of the country.
More importantly, it uses AES-256 encryption, which is what the United States government uses. This encryption makes it exceptionally secure.
ExpressVPN is limited to use on five devices. Prices will vary based on whether you pay month-to-month or several months at a time.
Pros:
- Large server network
- AES-256 encryption
- Secure and fast
Cons:
- Limited to five devices
NordVPN
NordVPN has around 5,000 servers in 60 countries. It includes special features such as multiple payment options, proxy extensions for some browsers, and DNS leak protection. Though not as user-friendly as some VPNs, NordVPN is a highly efficient option with above-average speed and performance.
NordVPN uses 2048-bit double encryption for maximum security. It can be used on up to six devices.
Pros:
- Large server network
- Fast
- Customizable
Cons:
- Difficult to use
Good news! I have a special deal for you!
Claim your deal now, I'm not sure how long it's going to last.
* By using the above links, you help make the internet a better place. If you decide to buy, this web page will be credited with a small commission, at NO EXTRA COST to you. Let's make the internet a better place, together!
* By using the above links, you help make the internet a better place. If you decide to buy, this web page will be credited with a small commission, at NO EXTRA COST to you. Let's make the internet a better place, together!
SurfShark
SurfShark is a simple but highly functional VPN and a great choice if you’re on a budget. It works across unlimited servers and devices, making it an even better value for the price. It’s fast and secure at a price you can afford.
Pros:
- Affordable
- AES-256 encryption
- Extra security features: IKEv2, private DNS, and DNS leak protection
Cons:
- Overly simple
CyberGhost
CyberGhost boasts a huge network of over 6,200 servers around the globe, making it fast and easy to use no matter where you are in the world. It comes with all the usual features including AES-256 encryption, DNS leak protection, and unlimited traffic and bandwidth. It can be used on up to seven devices and comes with a 45-day money-back guarantee.
Pros:
- Huge server network
- AES-256 encryption
- 45-day money-back guarantee
Cons:
- Expensive
IPVanish
IPVanish is a user-friendly option with lots of security features. It is one of the more inexpensive options on this list. It provides AES-256 encryption, several added security protocols, a SOCKS5 web proxy, and encrypted backup and storage. It can be used across an unlimited number of devices.
Pros:
- Easy to use
- Inexpensive
- Encrypted backup and storage
Cons
- Limited customer support
Conclusion
Though there are many potential security hazards of using public WiFi, there are nearly as many ways to protect yourself. Understanding the threats and taking steps to prevent security breaches will go a long way in reducing your chances of being victimized by identity theft, fraud, and viruses.
Share this with your friends
Related Articles
Here are some articles you might be interested in:
What questions do you have?
I make sure to answer them as soon as possible!
- Copyright © 2020 YOU are safe online.
- All Rights Reserved.